An Introduction to Steganography – Your Family Digital Photo may contain a Hidden Message

Steganography in cybersecurity today is no doubt a security concern. Afterall, the act of steganography is often associated with nefarious intent.
After reading this article, you can then ponder about the merits on the title of this article and draw your own conclusions on whether or not it is possible that your family digital photo may contain a hidden message. It is certainly a little far-fetched with the intent to create an attention-grabbing article title. Yet, it seems that the future with steganography is heading towards this reality.
Firstly, lets cover what exactly is steganography and the its basic concept. Considering at snapWONDERS we are mainly interested in photos, images, and video content we will use an image to demonstrate an example:
A Steganography Example
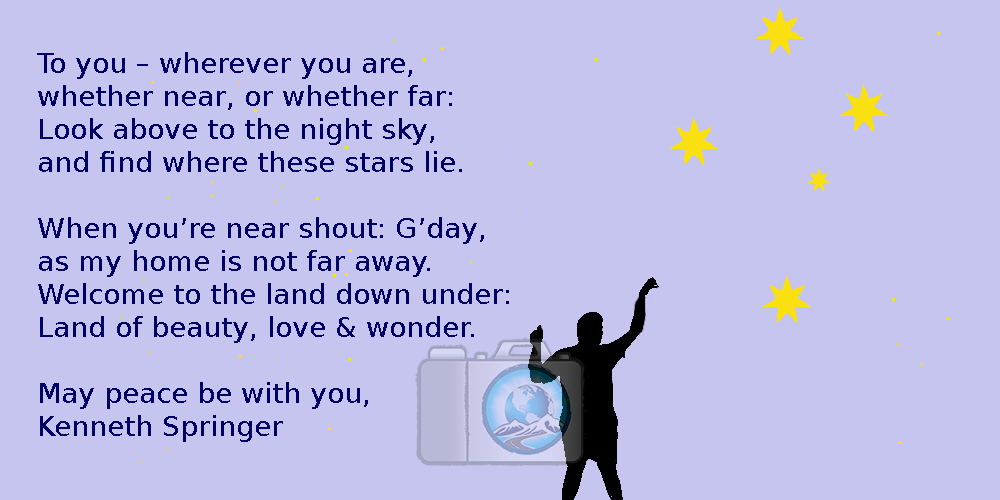
Imagine if there was a way to hide a secret message in what appears to be an image like the one below. The image contains a silhouette of my son (may his gentle soul rest in peace always) gazing at the night sky. I made the artwork and the illustration of the night sky with the stars.
In this example I chose an extremely simple technique with the goal to simply convey the concept of steganography. However, steganography techniques used today are extremely sophisticated and complex. It is also possible that some steganography techniques are in fact flying under the radar undetected and known only to its creators.

Can you see the message in the above image? Perhaps take a second look and look more closely as the message is plainly showing in the sky. If you are impatient you can scroll down to see the secret message revealed at the end of this article or keep reading with the hints provided throughout the article.
First Recorded use of Steganography
The first known use of steganography is traced back to 440BC in Greece with two recorded uses which involved:
- A Greek ruler shaving the head of his most trusted servant and marking the message onto his scalp and sending him to the destination when the hair was regrown concealing the message. Upon arrival to the destination and for the intended recipient the servant shaved the head revealing the message.
- A King of Sparta writing a secret message on plain wooden backing, in which was later covered with beeswax where a second message was etched onto the wax itself and thus concealing the first message. In those days, wax etching was a common form of writing method due to the ease of use. Upon arrival to the destination, and for the intended recipient the beeswax message was ignored and removed revealing the secret message under the wax.
Steganography in Digital media
In digital media the goal of steganography is to conceal a file, message, image, photo, sound or video within another file image, photo, or video. This is completely different to hidden metadata because the data itself in steganography is often encoded into the data itself, encrypted so it is unreadable and virtually hidden.
There are various steganography techniques that can be used, and some are briefly mentioned below. This article does not do any justice in covering the details as it is beyond the scope of an introduction article. The reality is each technique is complicated and often involves complicated mathematics and algorithms.
Common Steganography Techniques
Some common techniques in digital steganography is often in the form:
Palette Colour
The Palette Colour technique covers the above steganography example to illustrate the steganography concept. In simple terms it uses the differences amongst the colour palettes which is not detected by the human eye to conceal information.
Least Significant Bit (LSB)
This technique uses the Least Significant Bit of the information itself to carry the message payload. The image rendered to the human eye does not detect or hear (in the case of video sound) of the “hidden” payload of the message.
Depending on the size of the original image or video it is very possible to store and conceal a reasonably sized message.
Secure Cover Selection
The Secure Cover Selection technique is where you have the cover image that undergoes concealment of a secret message which yields a result exactly as the original image. The information is stored in areas within the cover image depending on the method used. Often concealed within the noisy areas of the image where the human eye cannot see the information.
Other techniques
Other steganography methods may be:
- Bit Plane Complexity (BPC)
- Histogram-based Data Hiding
- Pixel Value Differencing (PVD)
- Gray Level Modification Data (GLM)
- Steganographic in the DCT Domain
- Steganographic in the DWT Domain
- Steganographic in the DFT Domain
- Steganographic in the Contourlet Domain
- Compression Algorithm Technique
- Vector Quantization
The above is not the complete list of steganography techniques and these are ones we know about. It is generally accepted that there would be potentially many other techniques yet to be detected.
Steganography Objectives
The goal of steganography is not only to store a secret message that is undetectable in the digital media, but it is highly desirable if:
- The secret message can survive edits on the media itself. For example, some techniques may have part, or all the message survive if the image undergoes compression, cropping and resizing
- Is undetectable
- Can store large sized secret messages which can be decoded reliably
- Works in lossy or lossless images.
Practical Uses for Steganography
Now that you have some understanding on what steganography entails, it is extremely easy to see why steganography can be used for nefarious reasons. For instance, the leaking of confidential or proprietary information within the digital media that is intended for another party, or co-conspirator.
Or used for tracking purposes which is the case of digital watermarking. The concept is basically to embed a secret watermark into the digital media itself in which the original author can unveil to prove its ownership. Or alternatively, if you had downloaded the digital media which had contained a unique digital watermark, then when it is forensically shown the the digital media resides at a particular location contains the unique digital watermark, then it can be concluded it was sourced from the same original download source.
In other instances, the digital media can just be a host to carry the secret message in which it is used to harbor code or instructions for malicious intent. For example, a worm or virus on its own may not be particularly hostile until it extracts the secret code or instructions from undetected digital media content.
So – what was the Secret Message in the Example Steganography above?
For the example image given above. There are two shades of blue for the sky in which is not detected by the human eyesight. If you select the outside “blue pixel” and change all occurrences of this colour to a lighter blue colour. You will obtain the result as shown below:
While the above illustration is not particularly useful, it does however, convey the real possibility that messages can be contained within a digital media.
The future of steganography is likely to see digital watermarking becoming more prevalent as it does provide an elegant way to prove digital media ownership. On that basis, it is probably likely that digital media in the future is likely to contain steganography in some form which may include the family photo.

